All about Volt Typhoon, the Chinese hacking group, ET Telecom

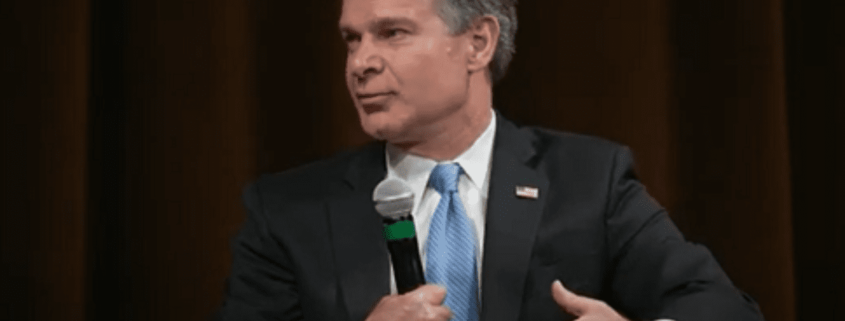
China is developing the “ability to physically wreak havoc” on US critical infrastructure and its hackers are waiting “for just the right moment to deal a devastating blow”, FBI Director Christopher Wray said on Thursday.
The comments were in relation to a Chinese government-linked hacking campaign dubbed Volt Typhoon. The campaign was disclosed by the US and its key allies in May 2023, when analysts at Microsoft found it had targeted everything from US telecommunication networks to transportation hubs.
On Thursday, Wray said Volt Typhoon had successfully gained access to American targets across the telecommunications, energy, water and other critical sectors.
Here is what is known about Volt Typhoon and its potential threat:
‘Future crises’
Nearly every country in the world uses hackers to gather intelligence. Major powers like the United States and Russia have large stables of such groups – many of which have been given colourful nicknames by cybersecurity experts, such as “Equation Group” or “Fancy Bear.”
Experts begin to worry when such groups turn their attention from intelligence gathering to digital sabotage. So when Microsoft Corp said in a blog post in May last year that Volt Typhoon was “pursuing development of capabilities that could disrupt critical communications infrastructure between the United States and Asia region during future crises,” it immediately brought to mind escalating tensions between China and the United States over Taiwan.
Any conflict between those two countries would almost certainly involve cyberattacks across the Pacific.
Taiwan botnet
Does this mean a group of destructive hackers is preparing to sabotage US infrastructure in the event of a conflict over Taiwan?
Microsoft qualified its assessment last year as “moderate confidence,” intelligence jargon that typically means a theory is plausible and credibly sourced but has yet to be fully corroborated. Different researchers have identified various aspects of the group.
It is now clear that Volt Typhoon has functioned by taking control of swathes of vulnerable digital devices around the world – such as routers, modems, and even internet-connected…