Tag Archive for: Exploitation
GoAnywhere MFT Zero-Day Exploitation Linked to Ransomware Attacks
/in Internet Security
The recent exploitation of a zero-day vulnerability in the GoAnywhere managed file transfer (MFT) software has been linked by a cybersecurity firm to a known cybercrime group that has likely attempted to exploit the flaw in a ransomware attack.
On February 1, Fortra alerted GoAnywhere MFT users about a zero-day remote code injection exploit. The vendor immediately provided indicators of compromise (IoCs) and mitigations, but released a patch only a week later.
Users, particularly those who are running an admin portal that is exposed to the internet, have been instructed to urgently install the patch.
There appear to be more than 1,000 internet-exposed instances of GoAnywhere. However, according to the vendor, exploitation requires access to the application’s admin console, and at least some of the exposed instances are associated with the product’s web client interface, which is not impacted.
No information was made available about the attacks exploiting the vulnerability, but managed endpoint detection and response firm Huntress reported this week that these attacks may have been conducted by a known cybercrime group. The company reached the conclusion after analyzing an attack detected in a customer environment on February 2.
Huntress has linked the attack to a malware family named Truebot, which was previously associated with a Russian-speaking threat actor named Silence. This group has also been linked to TA505, a threat group known for distributing the notorious Cl0p ransomware.
“Based on observed actions and previous reporting, we can conclude with moderate confidence that the activity Huntress observed was intended to deploy ransomware, with potentially additional opportunistic exploitation of GoAnywhere MFT taking place for the same purpose,” Huntress said in a blog post.
Cybersecurity firm Rapid7 has analyzed the vulnerability and assigned it the CVE identifier CVE-2023-0669. While the product does not belong to Rapid7, the company is a CVE Numbering Authority and it can assign CVEs to flaws found in the products of other vendors.
Related: Patch Tuesday: Microsoft Plugs Windows Hole Exploited in Ransomware Attacks
Related: Decade-Old Adobe ColdFusion…
VMware Says No Evidence of Zero-Day Exploitation in ESXiArgs Ransomware Attacks
/in Computer Security
VMware has urged customers to take action as unpatched ESXi servers continue to be targeted in ESXiArgs ransomware attacks.
Hackers are exploiting CVE-2021-21974, a high-severity ESXi remote code execution vulnerability related to OpenSLP that VMware patched in February 2021. Following successful exploitation, unidentified threat actors have deployed file-encrypting ransomware that targets virtual machines.
Technical details and a proof-of-concept (PoC) exploit for CVE-2021-21974 have been around for nearly two years, but there is no indication that in-the-wild exploitation has been observed until now.
In a blog post published on its Security Response Center on Monday, VMware said there is no evidence that the attacks involve exploitation of a zero-day vulnerability.
“Most reports state that End of General Support (EOGS) and/or significantly out-of-date products are being targeted with known vulnerabilities which were previously addressed and disclosed in VMware Security Advisories,” the virtualization giant said.
Attacks are possible because many organizations are running old and unpatched software.
“I’ve assessed nearly 500 owned boxes this evening, all of them are on old software releases. A shocking amount of orgs run ESXi on long end of life versions,” researcher Kevin Beaumont said on Monday.
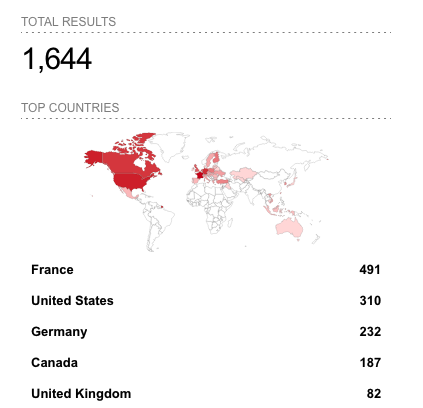
ESXiArgs ransomware attacks appear to have started on or around February 3. As of February 7, Censys shows nearly 2,500 compromised servers and Shodan shows more than 1,600. Most of the hacked systems are located in France, followed by the United States.
On compromised systems, the hackers drop a ransom note instructing victims to pay roughly $50,000 in bitcoins in order to recover their files and prevent them from getting leaked. While the cybercriminals claim to have stolen data that they will sell unless a ransom is paid, there does not appear to be any evidence to date that files have actually been stolen in ESXiArgs attacks.
As for the malware used in these attacks, it seems to target files associated with virtual machines.
In some cases, the malware’s encryption routine can partially fail, which could allow some victims to recover their data without…