Russia behind cyber attacks on Western utilities, security firm says | Yle News
“It’s kind of an escalation in that we’re seeing more than just data collection, surveillance and intelligence gathering,” Mikko Hyppönen says.

Russia has used malware in cyber attacks on targets in Eastern European countries since at least mid-2022, according to Finnish cyber security firm Withsecure.
More specifically, the company has reported that a Russian military intelligence effort led to the breach of databases belonging to an Estonian logistics company.
Finland’s eastern neighbour also appears to have tampered with water utility data systems in the US, France and Poland, according to Mandiant, a data security firm and subsidiary of Google.
So far, the cyberattacks do not appear to have caused significant disruptions. For example, the attack in the US caused a water tank at a facility in Texas to overflow until the system was brought under control, according to CNN.
But according to Withsecure’s research director, Mikko Hyppönen, it is a serious matter if Russia has started carrying out cyber attacks on Nato countries’ utilities.
“It’s kind of an escalation in that we’re seeing more than just data collection, surveillance and intelligence gathering,” Hyppönen told Yle.
Hyppönen: Russia attacked Estonian firm
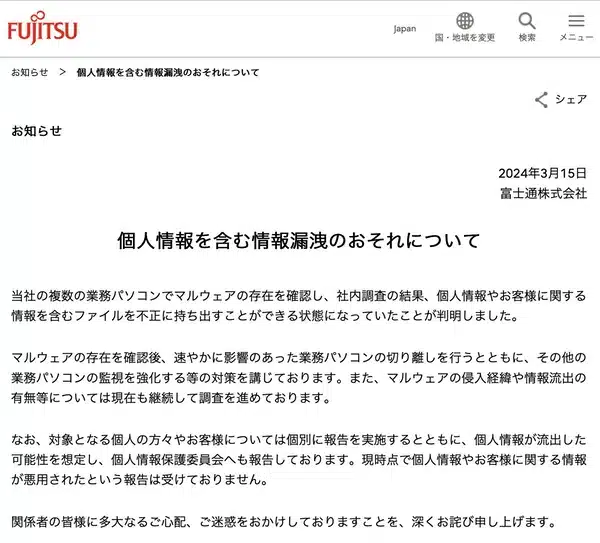
At the end of 2022 malicious code dubbed “Kapeka” helped hackers to breach a database belonging to an Estonian logistics firm. A recent study at Withsecure revealed who was behind the attack, according to Hyppönen.
“Our research linked the Kapeka malware directly to Russia’s Sandworm group, the country’s military cyber intelligence unit,” he explained.
The Sandworm group is known for having carried out several destructive attacks in Ukraine, including temporarily knocking out the war-torn country’s electricity grid.
“Kapeka’s development and deployment likely follow the ongoing Russia-Ukraine conflict, with Kapeka being likely used in targeted attacks of firms across Central and Eastern Europe since the illegal invasion of Ukraine in 2022,” a Withsecure brief on the matter explained.
According to Hyppönen, the Sandworm-delivered malware in Estonia caused disruptions at the…