Years later, the Ashley Madison hack remains an unsolved internet mystery

It’s downright strange how little we know about the hacker or hackers who exposed the identities of over 30 million Ashley Madison users in 2015. They leaked incredibly sensitive data about millions of people, did not profit in any obvious way, turned “Ashley Madison” into a punchline throughout the English speaking world, and rode off into the sunset.
You probably remember the hack, but it’s doubtful you remember the culprit: some entity called “The Impact Team.” A reward of $500,000 was offered for information leading to their arrest and prosecution, but no such arrest has ever been made.
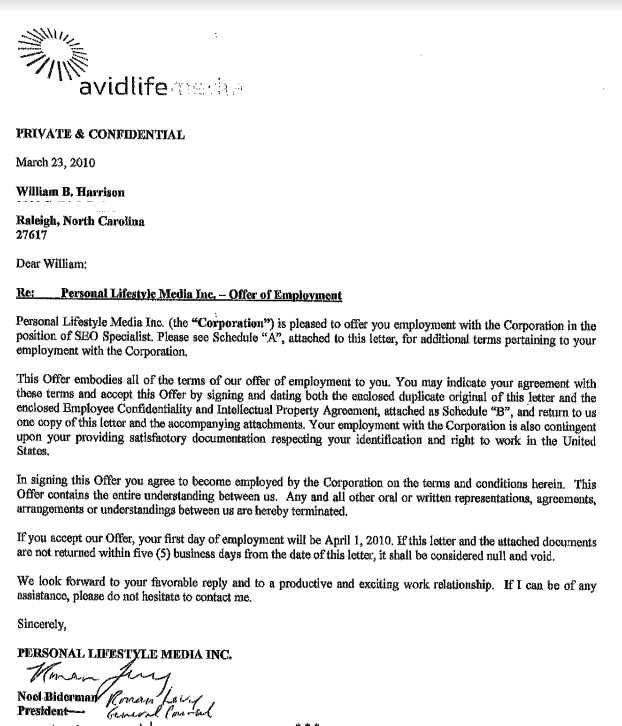
Noel Biderman, the CEO at the time of Ashley Madison’s parent company, claimed that he knew exactly who did it, and that they were an insider. But that turned out to have been a former employee who had died by suicide before the hack.
One possible culprit discovered by researchers at the time was an enigmatic figure calling himself Thadeus Zu. A Berkley researcher named Nicholas Weaver found the circumstantial evidence against Zu compelling enough to call upon law enforcement to get a warrant, crack open Zu’s social media accounts and find out more. That evidently never happened.
SEE ALSO: Google’s Bard AI chatbot is vulnerable to use by hackers. So is ChatGPT.
But Brian Krebs, the security researcher who initially reported the hack, and initially made the case against Thadeus Zu, uncovered an equally compelling person of interest earlier this year: Evan Bloom, a former Ashley Madison employee who was convicted in 2019 of selling hacked internet account information. In an interview with Krebs, Bloom denied involvement.
Without a guilty party able to give us the inside story on what happened, has the Ashley Madison hack been mis-shelved in the library of internet history? Have we all, in a sense, been swindled into accepting “LOL” as our collective response to something ugly and insidious?
Ashley Madison had long been an attractive target for hackers
To refresh your memory, Ashley Madison is (yep, is, not was) a paywalled dating website, founded in 2001, and marketed to people who are already in relationships — which is to say it’s ostensibly for linking…