8 secure file transfer services for the enterprise
The ability to securely share and synchronize files across systems is a cornerstone of enterprise IT. Millions of transfers occur every day, involving files of all types, sizes and structures.
At its most basic, file transfer technology moves data from one system to another system over a network. Unfortunately, legacy file transfer mechanisms, such as email and FTP, have historically lacked built-in security features.
Today’s organizations need confidence that file transfers will not compromise their data’s confidentiality, integrity and availability (CIA), the primary requirements of information security. The stakes are especially high in large-scale enterprises, where massive amounts of potentially sensitive information constantly move among internal and external users and systems. Secure file transfer services aim to protect an organization’s data while moving it from point A to point B.
How secure file transfer works
Secure file transfer services all have a common approach to protecting files: access control.
How this access control is achieved may vary widely among classes of products, not to mention individual products within each class. But the basic idea is that there is some sort of shared secret between the sender and the recipient. It could be as simple as a hard-to-guess URL transferred via email or an agreed-upon password. Or it could be as complex as integration with an enterprise identity and access management system. This shared secret is used to encrypt the file before it is transferred from the sender to the recipient. After getting the encrypted file, the recipient’s computer uses the shared secret to decrypt the file.
To meet the CIA requirements of today’s enterprises, secure file transfer services need a two-pronged approach:
- Secure data. The data itself should have embedded security. Encryption, for example, ensures no one else on a network can access, read or modify the contents of a file as it moves between systems.
- Secure delivery. Secure file transfer also involves some sort of reliable delivery, even if it’s just provided by TCP/IP Secure file transfer services use a variety of protocols and standards, ranging from established ones, such as Secure…


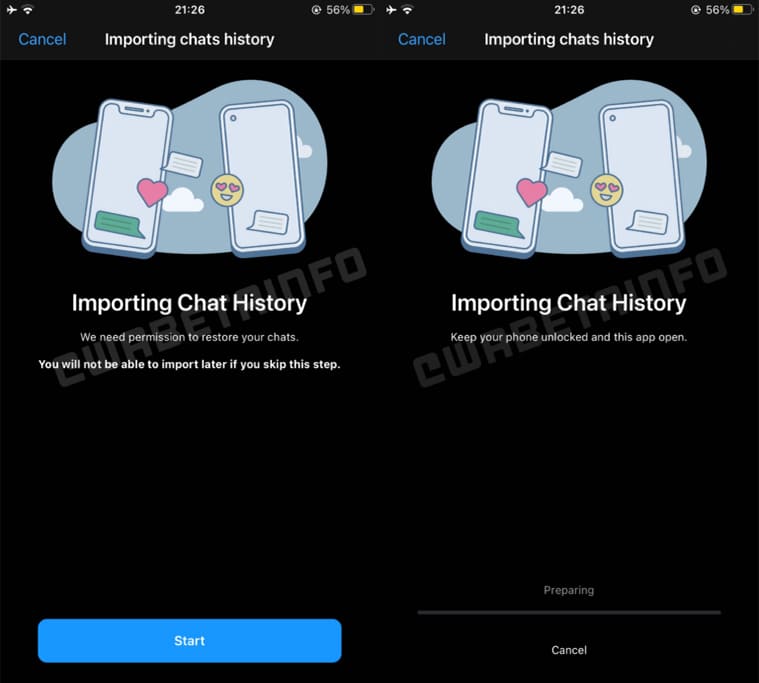 WhatsApp chat transfer prompt. (Image credit: WABetaInfo)
WhatsApp chat transfer prompt. (Image credit: WABetaInfo)