Ransomware Mastermind Uncovered After Oversharing on Dark Web
When researchers responded to an ad to join up with a ransomware-as-a-service (RaaS) operation, they wound up in a cybercriminal job interview with one of the most active threat actors in the affiliate business, who turns out to be behind at least five different strains of ransomware.
Meet “farnetwork,” who was unmasked after giving over too many specifics to a Group-IB threat researcher pretending to be a potential affiliate for the Nokoyawa ransomware group. The cybercriminal is also known by aliases including jingo, jsworm, razvrat, piparuka, and farnetworkit, the team learned.
After the undercover researcher was able to demonstrate they could execute privilege escalation, use ransomware to encrypt files, and ultimately demand cash for an encryption key, farnetwork was ready to talk details.
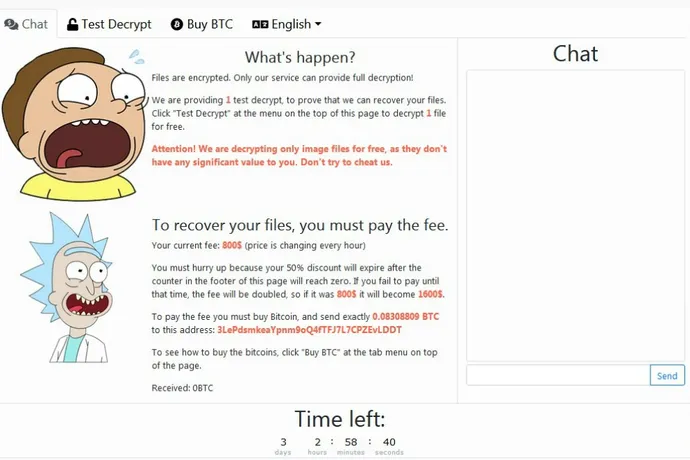
During the course of their correspondence, the Group-IB researcher learned farnetwork already had a foothold into various enterprise networks, and just needed someone to take the next step — i.e., to deploy the ransomware, and collect money. The deal would work like this, Group IB’s team learned: the Nokoyawa affiliate would get 65% of the extortion money, the botnet owner gets 20%, and the ransomware owner gets 15%.
But Nokayawa was just the latest ransomware operation farnetwork was running, Group-IB explained in its latest report. The threat actor ultimately gave over enough details for the team to trace farnetwork’s ransomware activities as far back as 2019.
Farnetwork bragged to the researchers about past operations with Nefilim and Karma ransomware, as well as being on the receiving end of ransomware payments as high as $1 million. The crook also mentioned past work with Hive and Nemty.
That was enough information for the Group-IB team to piece together a prolific ransomware resume in farnetwork’s past.
From 2019 to 2021, Group-IB said farnetwork was behind ransomware strains JSWORM, Karma, Nemty, and Nefilim. Nefilim’s RaaS program alone accounted for more than 40 victims, the report added.
By 2022, farnetwork found a home with the Nokoyawa operation, and by last February, was actively recruiting affiliates to the program.
“Based on the timeline of their operations,…