Cyber Security News Weekly Round-Up (Vulnerabilities, Cyber Attacks, Threats & New Stories)
Welcome to the Cyber Security News Weekly Round-Up. Each week, we will explore the latest cyber threats, vulnerabilities, and notable stories that have shaped the cybersecurity landscape.
From sophisticated malware attacks to innovative phishing schemes, we cover the crucial updates you need to stay informed and protected.
Threats
Notepad++ Plugin Compromised by Hackers
Hackers have targeted a widely used Notepad++ plugin, “mimeTools.dll,” injecting malicious code that compromises users’ systems upon execution. The attack, discovered by the AhnLab Security Intelligence Center, leverages DLL Hijacking to execute encrypted malicious Shell Code, posing a significant threat to programmers and writers who rely on Notepad++ for its versatility and plugin support; read more.
Weaponized PDF Files Deliver Byakugan Malware
Cybersecurity researchers at Fortinet have uncovered a new attack vector involving weaponized PDF files used to deliver the multi-functional Byakugan malware. By exploiting the trust and popularity of PDFs, hackers have been able to infiltrate systems through malicious codes embedded in seemingly innocuous documents, highlighting the need for heightened awareness and protection against such files.
Fake E-Shopping Attack Targets Banking Credentials
A sophisticated fake e-shop scam campaign has been targeting users in Southeast Asia, hijacking banking credentials through phishing emails and malicious APKs. The attackers have expanded their operations, utilizing screen-sharing and exploiting accessibility services to gain more control over victims’ devices. This campaign underscores the evolving tactics of cybercriminals in their efforts to steal sensitive information.
Rhadamanthys Stealer Targets Oil and Gas Sector
The oil and gas sector has become the latest target of the Rhadamanthys Stealer malware, delivered through weaponized PDF files. This attack emphasizes the ongoing threat to critical infrastructure sectors and the importance of robust cybersecurity measures to protect against such sophisticated threats.
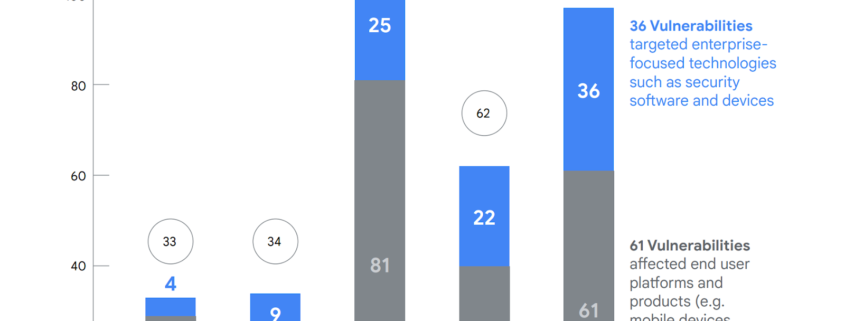
Ransomware Exploits Unpatched Vulnerabilities
A recent report highlights the increasing trend of ransomware attacks exploiting unpatched…