What is the Titan M2 security chip in Google’s Pixel phones?

With the Pixel 6 series, Google began developing its in-house Tensor SoC. But that wasn’t the first time the search giant used a piece of custom silicon in its smartphones – the Pixel 2’s Pixel Visual Core was technically the first. One generation later, the company announced that Pixel 3 devices would include a hardware security module dubbed Titan M. Then, in 2021, Google followed it up with the Titan M2. The security chip has since become a selling point for Google phones like the Pixel 8 series.
So in this article, let’s take a closer look at the role of the Titan M2 in Pixel devices, how it works, and why it’s even necessary in the first place.
What is the Titan M2 chip all about?
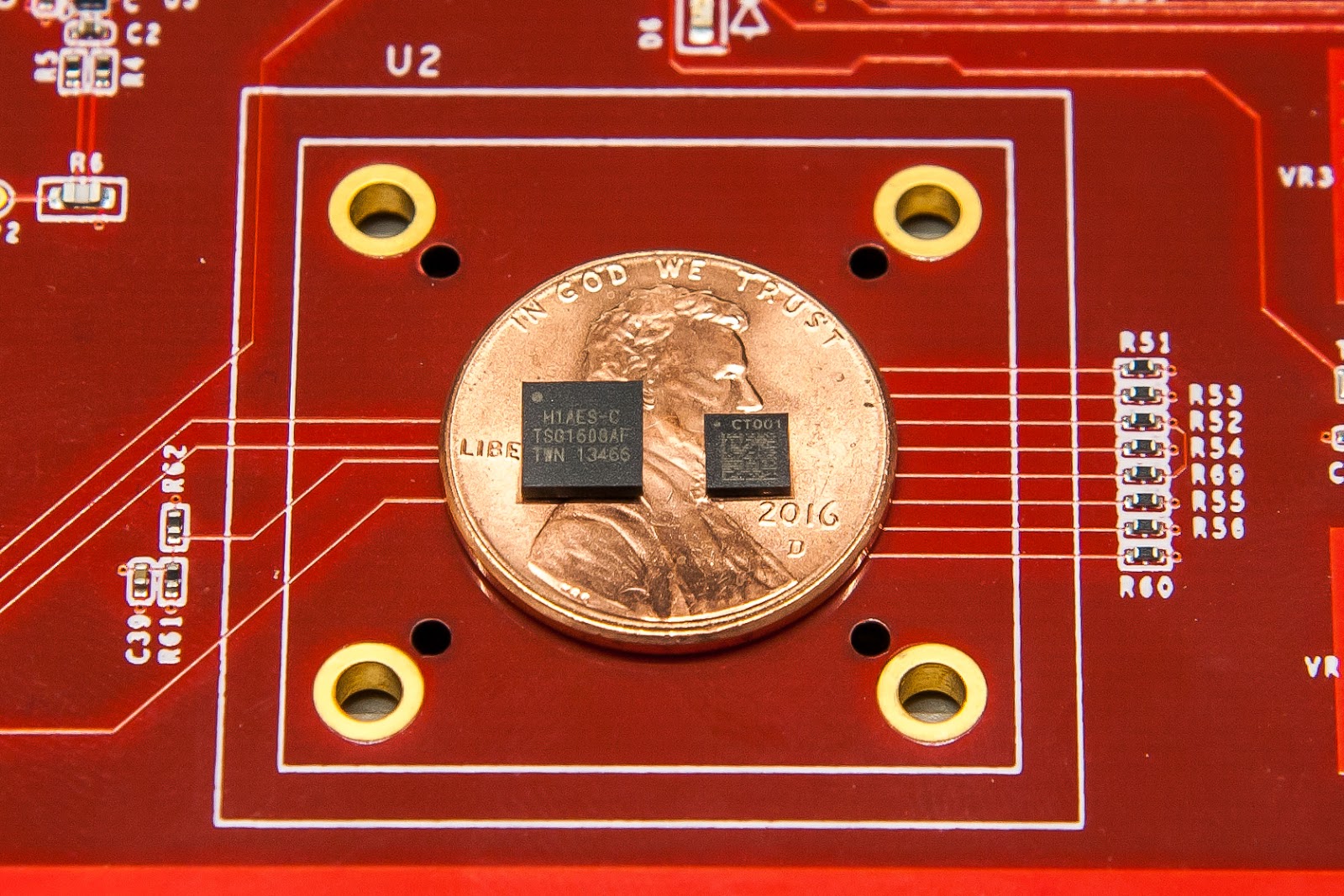
Google’s Titan server chip (left) and first-generation Titan M security chip (right)
The Titan M2 is a dedicated security chip included in Pixel 6 and Pixel 7 series smartphones. You’ll also find it in some other Google products like the Pixel Tablet. Google designed the Titan M2 in-house so that it could exercise complete control over its feature set. The chip is based on the RISC-V CPU architecture and contains its own memory, RAM, and cryptographic accelerator.
The Titan M2 is one of the many measures Google has employed to improve smartphone security over the years. The company uses the chip in its Pixel phones to provide an additional layer of protection on top of Android’s default security measures.
Google designed the Titan M2 chip to augment Android’s default security measures.
Take Android’s mandatory full-disk encryption. On most devices, it relies on a security feature known as a Trusted Execution Environment (TEE), which is essentially the secure area of a processor. Android devices store their encryption keys within this secure area, which is in turn guarded with your pattern, PIN, or passcode. In other words, the TEE isolates cryptographic keys and never reveals them to the user or even the operating system.
Virtually all smartphone SoCs in this day and age have a TEE or similar secure environment. On Snapdragon chips, it’s commonly referred to as the Qualcomm Secure Execution Environment (QSEE). Apple’s Arm-based chips like the M1 have the Secure Enclave. With these…

