Will your anti-fraud strategy prevent hacking?
The Herald

Tom Muleya Fraud Insight
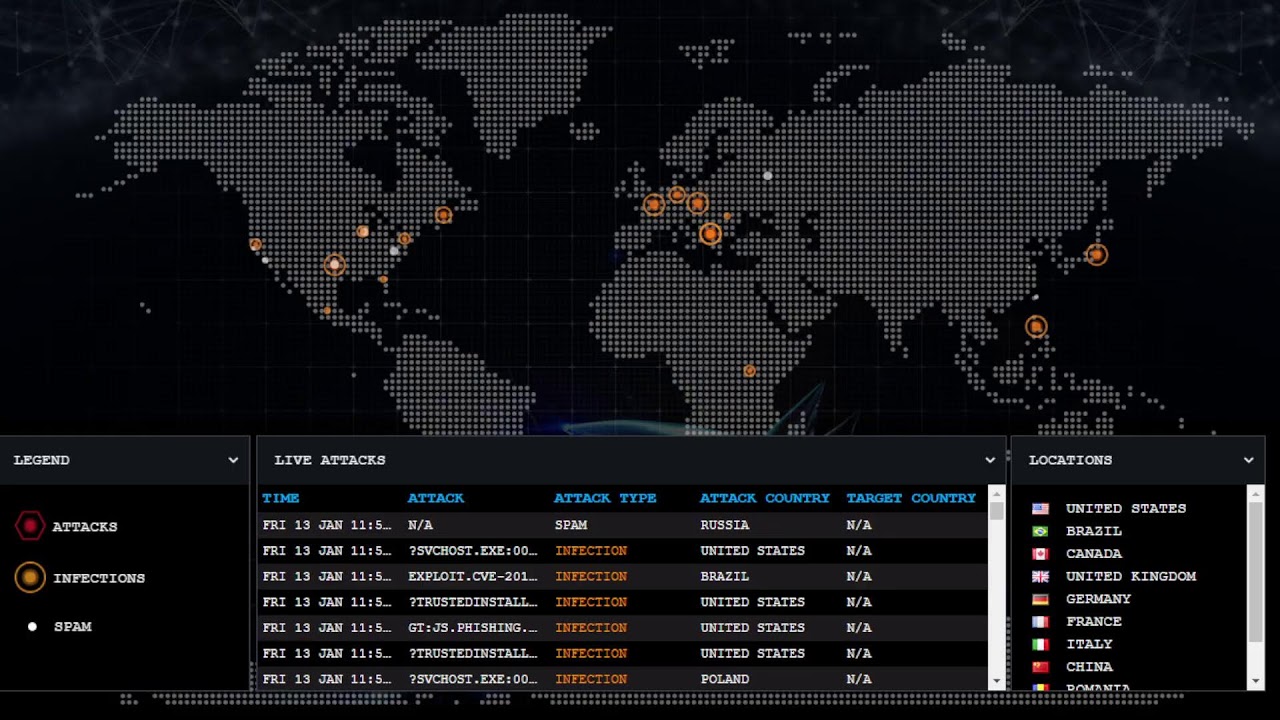
Cyber hacking has emerged to be one of the global problematic crimes in the 21st century to both the corporate world and individuals.
How the private sector, public sector, and individuals will be able to deal with this monster remains a big question! With the internet becoming central part of daily life, hacking is also becoming more sophisticated than ever before as new cyber threats are emerging on a regular basis.
Due to ever advancing technology and sophistication of computer crimes, Government had to craft the Data Protection Act to amend Sections (163-167) of the Criminal Law Codification and Reform Act.
Previously it was impossible for the law to adequately provide all essential elements needful to prosecute for a cybercrime case such as hacking. In the new Data Protection Act, hacking is one of the cybercrimes enshrined in the Act.
Computer hacking will give many organisations headache during this year 2023 and beyond. At the start of this year, CID Commercial Crimes Division received reports of cyber hacking of corporate organisations involving many millions of Zimbabwean dollars, thanks to the ZRP’s vigilant officers, detectives were quick to arrest some syndicates in these cases. The culprits have since appeared before the criminal courts.
In the previous article, we looked at the issue of implementing a sound and effective anti-fraud strategy to reduce cyber related crimes at organisations regardless of industry and size. Any organisation that will put in place and implement an effective anti-fraud strategy will be able to detect cyber incidences at an earliest possible time and will be able to quickly respond to crimes such as hacking.
Hacking refers to activities that seek to compromise digital devices, such as computers, smartphones, tablets, and even entire networks.
It is an act of identifying and then exploiting weaknesses or vulnerabilities in a computer system or network, usually with intent access to personal or organisational data such as financial information.
Cyber hackers employ a variety of techniques to hack their victims that include among others ‘social engineering’, password hacking (brute force attack),…