WoofLocker Toolkit Hides Malicious Codes in Images to Run Tech Support Scams
Cybersecurity researchers have detailed an updated version of an advanced fingerprinting and redirection toolkit called WoofLocker that’s engineered to conduct tech support scams.
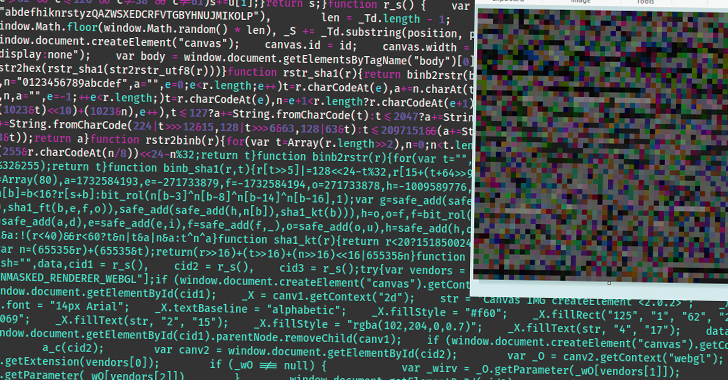
The sophisticated traffic redirection scheme was first documented by Malwarebytes in January 2020, leveraging JavaScript embedded in compromised websites to perform anti-bot and web traffic filtering checks to serve next-stage JavaScript that redirects users to a browser locker (aka browlock).
This redirection mechanism, in turn, makes use of steganographic tricks to conceal the JavaScript code within a PNG image that’s served only when the validation phase is successful. Should a user be detected as a bot or not interesting traffic, a decoy PNG file without the malicious code is used.
WoofLocker is also known as 404Browlock due to the fact that visiting the browlock URL directly without the appropriate redirection or one-time session token results in a 404 error page.
The cybersecurity firm’s latest analysis shows that the campaign is still ongoing.

“The tactics and techniques are very similar, but the infrastructure is now more robust than before to defeat potential takedown attempts,” Jérôme Segura, director of threat intelligence at Malwarebytes, said.
“It is just as difficult to reproduce and study the redirection mechanism now as it was then, especially in light of new fingerprinting checks” to detect the presence of virtual machines, certain browser extensions, and security tools.
A majority of the sites loading WoofLocker are adult websites, with the infrastructure using hosting providers in Bulgaria and Ukraine that give the threat actors stronger protection against takedowns.
The primary goal of browser lockers is to get targeted victims to call for assistance to resolve (non-existent) computer problems and gain remote control over the computer to draft an invoice that recommends affected individuals to pay for a security solution to address the problem.
“This is handled by third-parties via fraudulent call centers,” Segura noted back in 2020. “The threat actor behind the traffic redirection and browlock will get paid for each successful…