‘Anatsa’ malware targets banking users in US, UK and Central Europe
A mobile malware campaign targeting banking apps has been observed targeting users in the U.S., the U.K. and Central Europe.
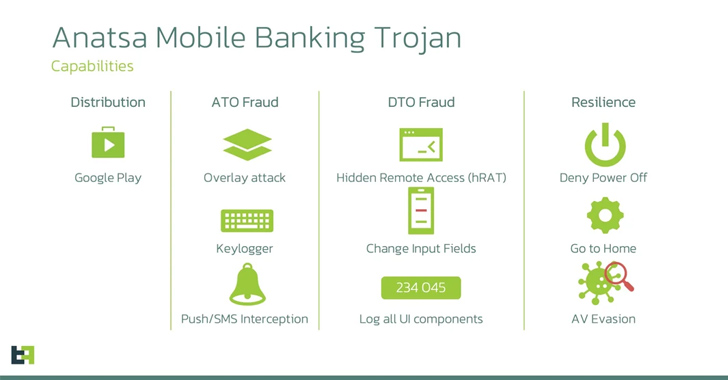
Dubbed “Anatsa” by researchers at ThreatFabric B.V., the banking Trojan is distributed through malicious apps in the Google Play Store and is estimated to have had over 30,000 installations since March. Anatsa has advanced device-takeover capabilities that can circumvent existing fraud control mechanisms.
The malware is said to have been active since 2020 but has shifted focus over the years, with the current campaign targeting banking apps, particularly in Germany. According to the researchers, Anatsa’s target list includes almost 600 financial applications worldwide, with the malware stealing customers’ mobile banking application credentials to initiate fraudulent transactions.
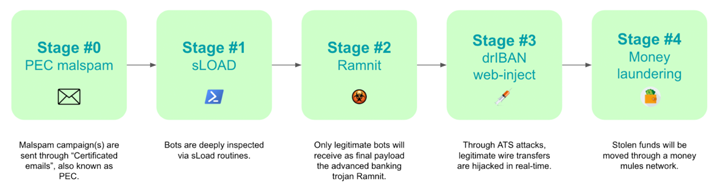
Once installed, Anatsa makes a request to a page hosted on GitHub, where the dropper obtains a URL to download the payload, also hosted on GitHub. The payloads masquerade as an add-on to the original application.
After first detecting the campaign in March, the ThreatFabric researchers reported it to Google and it was removed from the Play Store. However, a month later, those behind Anatsa returned with a new app posing as a PDF viewer, with the malware masquerading as an add-on.
The researchers note that the choice of disguise for these malicious applications observed confirms the trend seen for droppers on Google Play. Droppers tend to impersonate file-management-related applications.
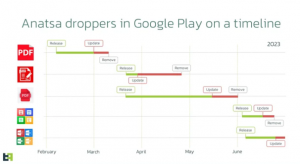 The new app was reported to Google again and removed, but in the ultimate game of Whac-A-Mole, every time the apps were removed, new apps appeared. The researchers note that the speed at which the actors return with a new dropper after the previous one is removed is notable in itself, given that the coding can take anywhere from a few days and several weeks.
The new app was reported to Google again and removed, but in the ultimate game of Whac-A-Mole, every time the apps were removed, new apps appeared. The researchers note that the speed at which the actors return with a new dropper after the previous one is removed is notable in itself, given that the coding can take anywhere from a few days and several weeks.
“It is crucial for companies to remain vigilant regarding the ever-evolving capabilities of attackers who constantly innovate their methodologies,” Pedro Fortuna, co-founder and chief technology officer of JaveScript protection company Jscrambler S.A., told SiliconANGLE. “Similarly, users must exercise caution when…