Windows-based ransomware now infects Linux devices as well
A ransomware variant commonly known for encrypting Windows systems has recently been found targeting Linux devices as well.
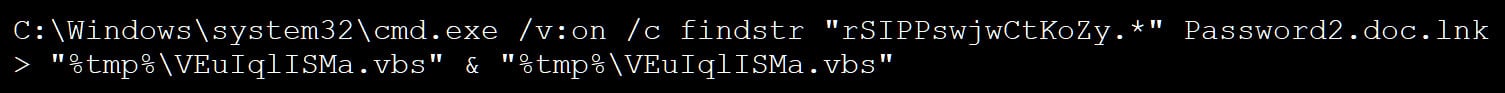
According to a report by SentinelLabs, Linux versions of the ransomware strain IceFire have recently compromised the networks of several media and entertainment sector organizations worldwide. The operators behind the ransomware do this by exploiting a deserialization vulnerability in the IBM Aspera Faspex file-sharing software. After gaining access to the victim’s system, they will then deploy the IceFire ransomware, which will encrypt data and append the ‘.ifire’ extension to the affected files. The ransomware will finally delete itself to cover its tracks.
Interestingly enough, IceFire doesn’t encrypt all files on Linux. It actually avoids encrypting certain paths to ensure that critical parts of the system will remain operational and avoid further damage to the system.
Once the ransomware completes data encryption, it will drop a ransom note which asks the victim to contact the malware’s operators within five days. If they fail to do so, the note claims that the victim’s data will be publicly posted online.
IceFire is just one of many ransomware variants that have started targeting Linux systems. “While the groundwork was laid in 2021, the Linux ransomware trend accelerated in 2022 when illustrious groups added Linux encryptors to their arsenal,” SentinelLabs’ blog stated. Some of these variants include Conti, LockBit, Hive, and HelloKitty, among others.