Valorant aimbot hack lures the unwary into malware infection • Graham Cluley

Just what would you do to be better at video games? Devote yourselves to hundreds of hours of practice, or search the internet for cheats and hacks that might give you an unfair competitive advantage.
Cheating in online games is nothing new, and some players have no qualms about resorted to installing “aimbots” that might help them by automatically aiming at their fellow rivals or even auto-shoot.
However, as South Korean security experts at AhnLab warn, you might be wise to resist the temptation to cheat.
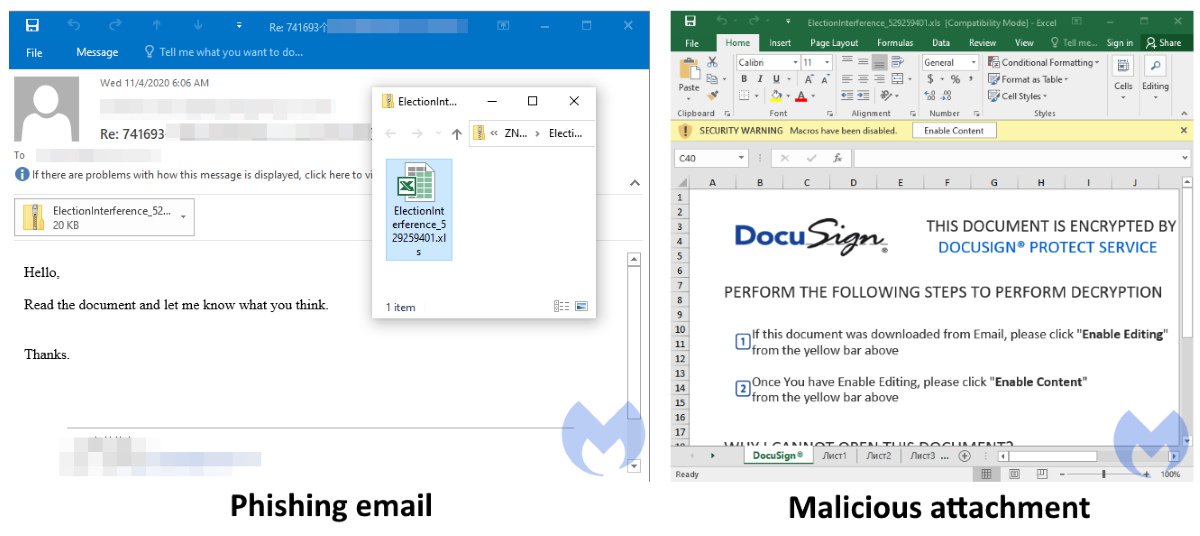
According to the security researchers, malware has been distributed via descriptions in a YouTube video related to the Valorant first person shooter game.
The video’s description cheekily advises users to disable their anti-virus software before downloading the cheat (boy… the things people will do if they think it will improve their aim in a video game.)
FREE CHEAT = <LINK>
if link dont work – Try VPN
TURN OFF ANTI VIRUS
The YouTube video’s description contains a link which points to a website containing a file called Pluto Valrant cheat.rar.
If you’re unlucky enough to be duped into downloading the .RAR archive file, and then run the enclosed executable (named Cheat Installer.exe), your computer will be infected with an information-stealing Trojan horse called RedLine.
According to the AhnLab researchers, the malware collects a wide array of information from infected Windows systems, including login credentials, Discord tokens, Steam and Telegram session files, cryptocurrency wallets, and more.
The stolen data is then sent to cybercriminals via a Discord server.
As ever you should be highly suspicious of software of unknown provenance, and links to downloads from YouTube videos. It should go without saying that if you’re ever advised to disable your anti-virus, steer well clear!
Many of us might need a helping hand to defeat our video game rivals, but you could end up shooting yourself in the foot.
Found this article interesting? Follow Graham Cluley on Twitter to read more of the exclusive content we post.