‘Zero-Click’ hacks are growing in popularity. There’s practically no way to stop them
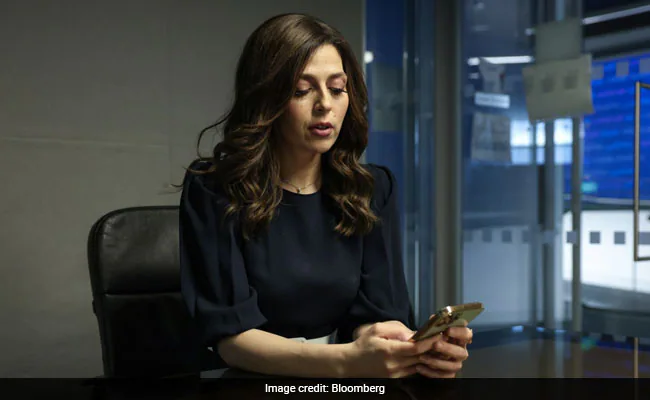
As a journalist working for the Arab news network Alaraby, Rania Dridi said she’s taken precautions to avoid being targeted by hackers, keeping an eye out for suspicious messages and avoiding clicking on links or opening attachments from people she doesn’t know.
Dridi’s phone got compromised anyway with what’s called a “zero-click” attack, which allows a hacker to break into a phone or computer even if its user doesn’t open a malicious link or attachment. Hackers instead exploit a series of security flaws in operating systems — such as Apple Inc.’s iOS or Google’s Android — to breach a device without having to dupe their victim into taking any action. Once inside, they can install spyware capable of stealing data, listening in on calls and tracking the user’s location.
With people more wary than ever about clicking on suspicious links in emails and text messages, zero-click hacks are being used more frequently by government agencies to spy on activists, journalists and others, according to more than a dozen surveillance company employees, security researchers and hackers interviewed by Bloomberg News.
Once the preserve of a few intelligence agencies, the technology needed for zero-click hacks is now being sold to governments by a small number of companies, the most prominent of which is Israel’s NSO Group. Bloomberg News has learned that at least three other Israeli companies — Paragon, Candiru and Cognyte Software Ltd. — have developed zero-click hacking tools or offered them to clients, according to former employees and partners of those companies, demonstrating that the technology is becoming more widespread in the surveillance industry.
There are certain steps that a potential victim can take that might reduce the chances of a successful zero-click attack, including keeping a device updated. But some of the more effective methods — including uninstalling certain messaging apps that hackers can use as gateways to breach a device — aren’t practical because people rely on them for communication, said Bill Marczak, a senior research fellow at Citizen Lab, a research group at the University of Toronto that focuses on abuses of surveillance…