Cyber engineering, computer science team publishes a paper and presents research on popular app vulnerabilities
Hacking a safety app netted a Louisiana Tech University Computer Science graduate student a publishing credit, a trip to Hawaii, and the opportunity to present the research at an international conference.
Louisiana Tech Cyber Engineering alumnus and current MS Computer Science and CyberCorps ®: Scholarship for Service student Jonah Fitzgerald (‘22), along with fellow Cyber Engineering program alumni Thomas Mason (‘22) and Brian Mulhair (‘22), discovered a vulnerability in the Louisiana Department of Health COVID Defense contact tracing app that allows hackers to attack neighboring devices.
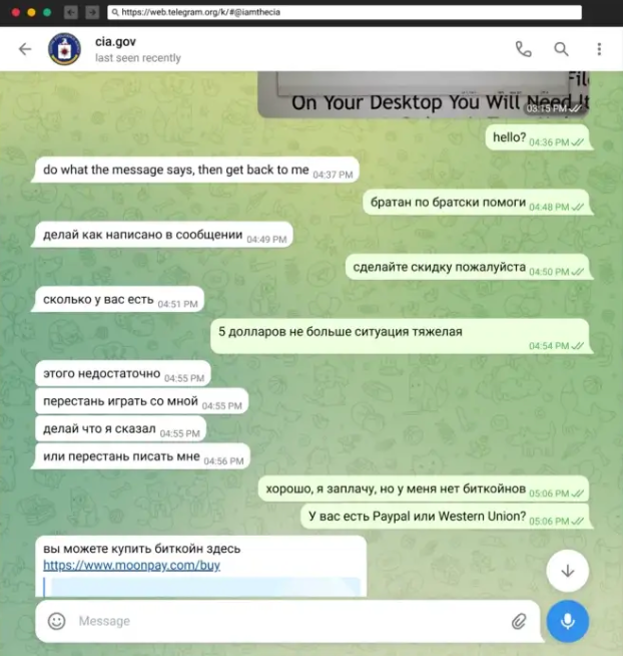
As seniors researching a paper assignment for Dr. William Bradley Glisson’s Computer Science 448/543, Cyber Engineering 404 “Reverse Engineering” class, the team discovered the symptoms history share feature of the app could be modified to send a malicious link via email, WIFI, and nearby share systems. The team was able to demonstrate two attacks using the link: They were able to harvest credentials by redirecting users to a fake page resembling the My.LA.Gov page and installing an Android app on the target phone to access all the information in that phone.
With additional guidance from Glisson, the team improved their results, presented the research to Glisson’s Cybersecurity Information Technology Exploration Research Group, and submitted the paper to the conference.
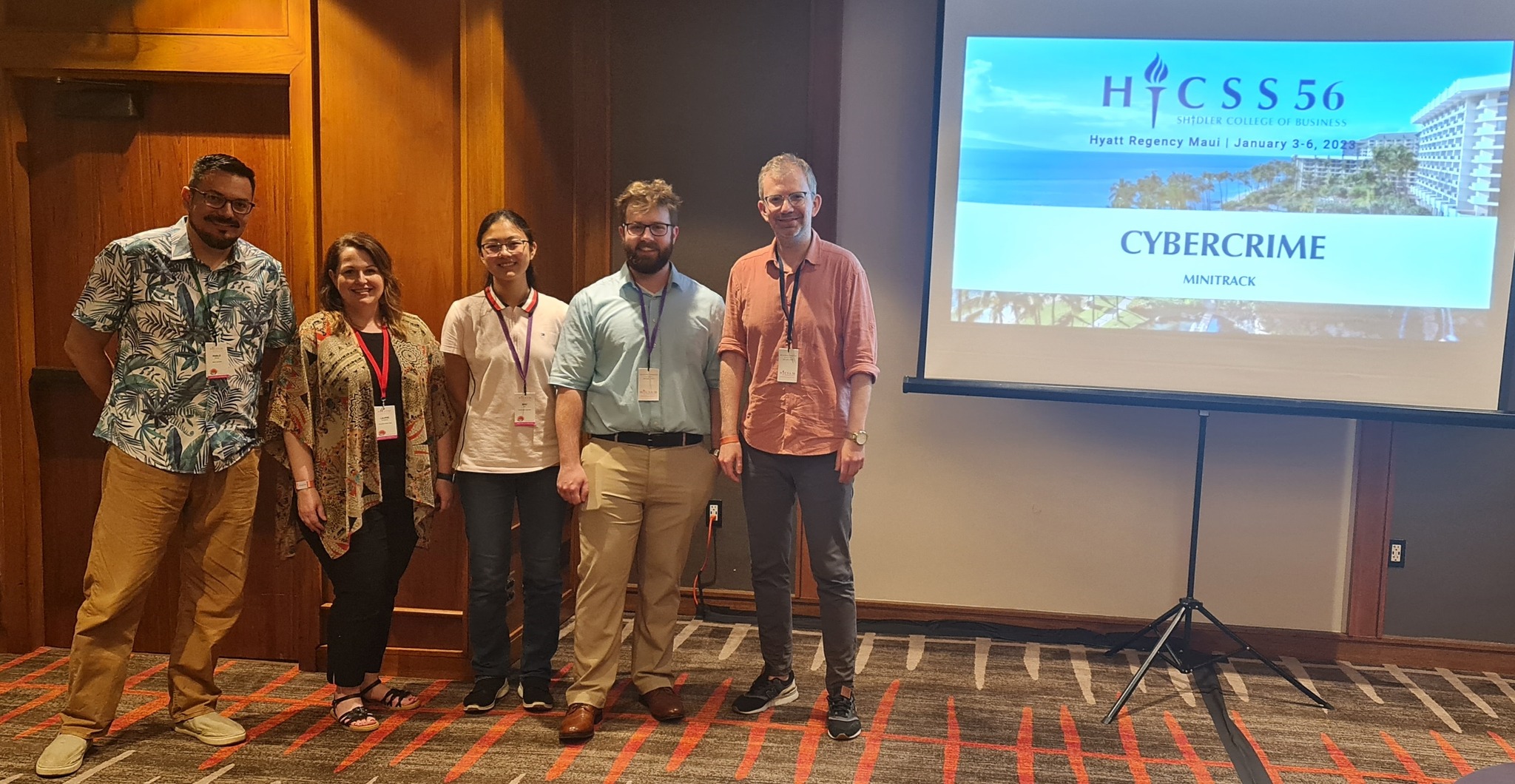
Fitzgerald then had the opportunity to travel to Ka’anapali Beach on the island of Maui to present the team’s findings at the 56th Hawaii International Conference on System Sciences “Internet and the Digital Economy” track and “Cybercrime” mini-track.
“I wanted to get involved with this research because I felt I could make a meaningful contribution to improving mobile app security and fighting the COVID-19 pandemic,” Fitzgerald said. “I feel that my Tech education in cyber engineering prepared me for success in solving these types of problems by rapidly learning new concepts like reverse engineering and tackling tough challenges in cybersecurity and computer science.”
Fitzgerald, who is continuing his graduate education with Louisiana Tech and is a member of the Louisiana Tech Research…